PRTG Manual: Root Group Settings
The root group is the highest instance in the object hierarchy and it is the parent to most other objects. Therefore, most objects inherit settings from the root group. So, before you create your own sensors, it is a good idea to review the root group's settings to make sure that they suit your needs.
If necessary, you can override every setting for every single child object. To do so, disable the respective inherit from option of an object.
The following settings are available on the Settings tab. All of the settings that you define here can be inherited to all other objects in your setup.
This documentation refers to an administrator that accesses the PRTG web interface on a master node. Other user accounts, interfaces, or failover nodes might not have all of the options in the way described here. In a cluster, note that failover nodes are read-only by default.
In this section:
- Basic Group Settings
- Location
- Credentials for Windows Systems
- Credentials for Linux/Solaris/macOS (SSH/WBEM) Systems
- Credentials for VMware/XenServer
- Credentials for SNMP Devices
- Credentials for Database Management Systems
- Credentials for AWS
- Credentials for Microsoft 365
- Credentials for Script Sensors
- Windows Compatibility Options
- SNMP Compatibility Options
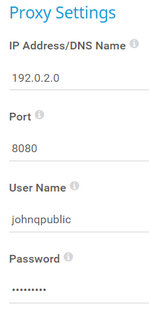
- Proxy Settings
- Scanning Interval
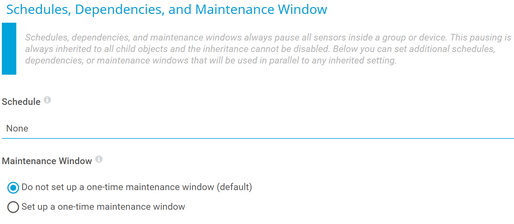
- Schedules, Dependencies, and Maintenance Window
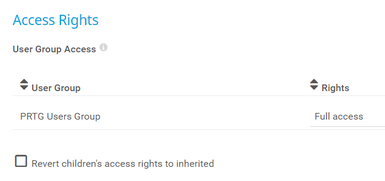
- Access Rights
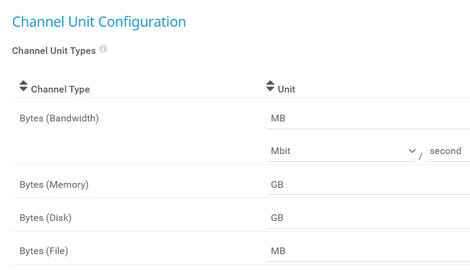
- Channel Unit Configuration
- Advanced Network Analysis
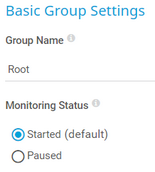
Setting |
Description |
|---|---|
Group Name |
Enter a name to identify the group. By default, PRTG displays it in the device tree.
|
Monitoring Status |
Select the monitoring status of the group:
|
Setting |
Description |
|---|---|
Location (for Geo Maps) |
If you want to use Geo Maps, enter a location in the first line. Geographical maps then display objects like devices or groups with a status icon using a color code similar to the sensor status icons (green–yellow–orange–red). You can enter a full postal address, city and country only, or latitude and longitude. It is possible to enter any text before, between, and after the coordinates, as PRTG automatically parses latitude and longitude, for example, enter 49.452778 11.077778, or enter 49.452778 any 11.077778 text. A minus sign (-) in the first line hides an object from a geographical map. In this case, you can enter location information in line two and following. You can define a specific label for each location. Enter a string denoting the label in the first line and provide the coordinates in the second line. This geographical marker then shows the object with the label in the geographical map.
|
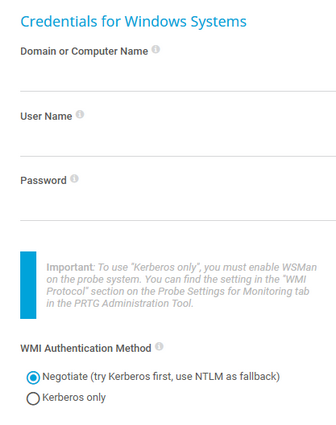
Credentials for Windows Systems
The settings you define in this section apply to the following sensors:
Setting |
Description |
|---|---|
Domain or Computer Name |
Enter the domain or computer name of the user account with which you want to access the Windows system. PRTG uses this account for Windows Management Instrumentation (WMI) sensors and other Windows sensors. If you want to use a Windows local user account on the target device, enter the computer name. If you want to use a Windows domain user account (recommended), enter the domain name. PRTG automatically adds a prefix to use the NT LAN Manager (NTLM) protocol if you do not explicitly define it. Do not leave this field empty.
|
User Name |
Enter the user name for access to the Windows system. Usually, you use credentials with administrator rights. |
Password |
Enter the password for access to the Windows system. Usually, you use credentials with administrator rights. |
WMI Protocol Used by the Classic Remote Probe |
Shows the WMI protocol that the parent probe device of this object uses for authentication. PRTG shows this setting for reference purposes only. You can change the protocol in the PRTG Administration Tool.
|
WMI Authentication Method |
Define how a probe authenticates with Windows systems:
|
Credentials for Linux/Solaris/macOS (SSH/WBEM) Systems
The settings you define in this section apply to the following sensors:
- SSH Disk Free
- SSH Disk Free v2
- SSH INodes Free v2
- SSH Load Average v2
- SSH Meminfo v2
- SSH Remote Ping v2
- SSH SAN Enclosure
- SSH SAN Logical Disk
- SSH SAN Physical Disk
- SSH SAN System Health
- SSH Script
- SSH Script v2
- SSH Script Advanced
- VMware Host Hardware (WBEM)
Setting |
Description |
|---|---|
User Name |
Enter the user name for access to the Linux/Solaris/macOS system via Secure Shell (SSH) and Web-based Enterprise Management (WBEM). Usually, you use credentials with administrator rights. |
Authentication Method |
Select the authentication method for the login:
|
Password |
This setting is only visible if you select Password above. Enter a password for access to the Linux/Solaris/macOS system via SSH and WBEM. Usually, you use credentials with administrator rights. |
Private Key |
This setting is only visible if you select Private key above. Paste the entire RSA private key, including the BEGIN and END lines. Make sure that a corresponding public key exists on the target device.
|
WBEM Protocol |
Select the protocol that you want to use for the connection to the system via WBEM:
|
WBEM Port |
Select if you want to use one of the default ports for the connection to the system via WBEM or if you want to set a custom port:
|
Custom WBEM Port |
This setting is only visible if you select Custom above. Enter a custom WBEM port. Enter an integer. |
SSH Port |
Enter the port for SSH connections. Enter an integer. The default port is 22.
|
SSH Rights Elevation |
Select the rights that you want to use to run the command on the target system:
|
Target System User Name |
This setting is only visible if you select an option that includes sudo or su above. Enter a user name to run the specified command on the target system as a different user than the root user. If you leave this field empty, you run the command as a root user. Make sure that you set the Linux password even if you use a public key or a private key for authentication. This is not necessary if the user is allowed to run the command without a password. |
Password |
This setting is only visible if you select an option that includes sudo or su with password above. Enter the password to run the sudo command or the su command. |
SSH Connection Mode |
Select the connection mode that you want to use to access data with SSH sensors:
|
Credentials for VMware/XenServer
The settings you define in this section apply to the following sensors:
- Citrix XenServer Host
- Citrix XenServer Virtual Machine
- VMware Datastore (SOAP)
- VMware Host Hardware (WBEM)
- VMware Host Hardware Status (SOAP)
- VMware Host Performance (SOAP)
- VMware Virtual Machine (SOAP)
Setting |
Description |
|---|---|
User Name |
Enter the user name for access to VMware ESXi, vCenter Server, or Citrix XenServer. Usually, you use credentials with administrator rights. |
Password |
Enter the password for access to VMware ESXi, vCenter Server, or Citrix XenServer. Usually, you use credentials with administrator rights.
|
VMware Protocol |
Select the protocol for the connection to VMware ESXi, vCenter Server, or Citrix XenServer:
|
Session Handling |
Select if you want to reuse a session for VMware sensors:
|
The settings you define in this section apply to the following sensors:
Setting |
Description |
|---|---|
SNMP Version |
Select the Simple Network Management Protocol (SNMP) version for the connection to the target SNMP device:
|
Community String |
This setting is only visible if you select SNMP v1 or SNMP v2c (default) above. Enter the community string of your device. This is like a clear-text password for simple authentication.
|
Authentication Method |
This setting is only visible if you select SNMP v3 above. Select the authentication method:
|
User Name |
This setting is only visible if you select SNMP v3 above. Enter the user name for access to the target SNMP device.
|
Password |
This setting is only visible if you select SNMP v3 above. Enter the password for access to the target SNMP device.
|
Encryption Type |
This setting is only visible if you select SNMP v3 above. Select an encryption type:
|
Encryption Key |
This setting is only visible if you select SNMP v3 above. Enter an encryption key. If you provide a key, PRTG encrypts SNMP data packets with the encryption algorithm that you selected above. Leave this setting blank if you select None for the Encryption Type. Enter a string or leave the field empty.
|
Context Name |
This setting is only visible if you select SNMP v3 above. Enter a context name only if the configuration of the device requires it. Context is a collection of management information that is accessible by an SNMP device. Enter a string. |
SNMP Port |
Enter the port for the connection to the SNMP target device. Enter an integer. The default port is 161.
|
Timeout (Sec.) |
Enter a timeout in seconds for the request. Enter an integer. The maximum timeout value is 300 seconds (5 minutes). |
Credentials for Database Management Systems
The settings you define in this section apply to the following sensors:
Setting |
Description |
|---|---|
Port |
Select the port that PRTG uses for connections to the monitored databases:
|
Custom Port |
Enter a custom port for database connections. Enter an integer.
|
Authentication Method |
Select the authentication method for the connection to the Structured Query Language (SQL) database:
|
User Name |
This setting is only visible if you select SQL server authentication above. Enter the user name for the database connection. |
Password |
This setting is only visible if you select SQL server authentication above. Enter the password for the database connection. |
Timeout (Sec.) |
Enter a timeout in seconds for the request. Enter an integer. The maximum timeout value is 900 seconds (15 minutes). |
The settings you define in this section apply to the following sensors:
For more information about the permissions that are necessary to query the AWS API, see the Knowledge Base: How do I set permissions for the Amazon Web Services (AWS) API key to use certain sensors in PRTG?
Setting |
Description |
|---|---|
Access Key ID |
Enter the Amazon Web Services (AWS) access key ID. |
Secret Access Key |
Enter the AWS secret access key. |
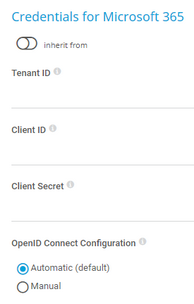
The settings you define in this section apply to the following sensors:
The sensors use the credentials to authenticate with Microsoft Entra ID.
For more information about the credentials and the permissions that are necessary to use the Microsoft 365 Service Status sensor and the Microsoft 365 Service Status Advanced sensor, see the Knowledge Base: How do I obtain credentials and set permissions for the Microsoft 365 Service Status sensors?
For more information about the credentials and the permissions that are necessary to use the Microsoft 365 Mailbox sensor, see the Knowledge Base: How do I obtain credentials and set permissions for the Microsoft 365 Mailbox sensor?
Setting |
Description |
|---|---|
Tenant ID |
Enter the Microsoft Entra tenant ID.
|
Client ID |
Enter the Microsoft Entra client ID. |
Client Secret |
Enter the Microsoft Entra client secret. |
OpenID Connect Configuration |
Select if you want to manually enter the authorization endpoint URL and token endpoint URL that PRTG uses to access Microsoft Graph:
|
Authorization Endpoint |
Enter the authorization endpoint URL including the server. Authorization endpoint URL example: https://login.microsoftonline.com/<tenant-ID>/oauth2/v2.0/authorize
|
Token Endpoint |
Enter the token endpoint URL including the server. Token endpoint URL example: https://login.microsoftonline.com/<tenant-ID>/oauth2/v2.0/token
|
Credentials for Script Sensors
The settings you define in this section apply to the following sensors:
Setting |
Description |
|---|---|
Placeholder 1 Description |
Enter a description for Placeholder 1, for example information about the purpose or content of the placeholder. |
Placeholder 1 |
Enter a value for the placeholder. PRTG inserts the value for the script execution if you add %scriptplaceholder1 in the argument list. PRTG does not display the value in the sensor log or the sensor's settings. |
Placeholder 2 Description |
Enter a description for Placeholder 2, for example information about the purpose or content of the placeholder. |
Placeholder 2 |
Enter a value for the placeholder. PRTG inserts the value for the script execution if you add %scriptplaceholder2 in the argument list. PRTG does not display the value in the sensor log or the sensor's settings. |
Placeholder 3 Description |
Enter a description for Placeholder 3, for example information about the purpose or content of the placeholder. |
Placeholder 3 |
Enter a value for the placeholder. PRTG inserts the value for the script execution if you add %scriptplaceholder3 in the argument list. PRTG does not display the value in the sensor log or the sensor's settings. |
Placeholder 4 Description |
Enter a description for Placeholder 4, for example information about the purpose or content of the placeholder. |
Placeholder 4 |
Enter a value for the placeholder. PRTG inserts the value for the script execution if you add %scriptplaceholder4 in the argument list. PRTG does not display the value in the sensor log or the sensor's settings. |
Placeholder 5 Description |
Enter a description for Placeholder 5, for example information about the purpose or content of the placeholder. |
Placeholder 5 |
Enter a value for the placeholder. PRTG inserts the value for the script execution if you add %scriptplaceholder5 in the argument list. PRTG does not display the value in the sensor log or the sensor's settings. |
If you experience problems when you monitor via Windows sensors, use the following compatibility options for troubleshooting.
Setting |
Description |
|---|---|
Preferred Data Source |
Define the method that Windows sensors use to query data:
|
Timeout Method |
Select the time that the sensor waits for the return of the WMI query before the sensor cancels the query and shows an error message:
|
Timeout (Sec.) |
This setting is only visible if you select Set manually above. Enter the time the sensor waits for the return of its WMI query before it cancels it and shows an error message. Enter an integer. The maximum timeout value is 900 seconds (15 minutes). |
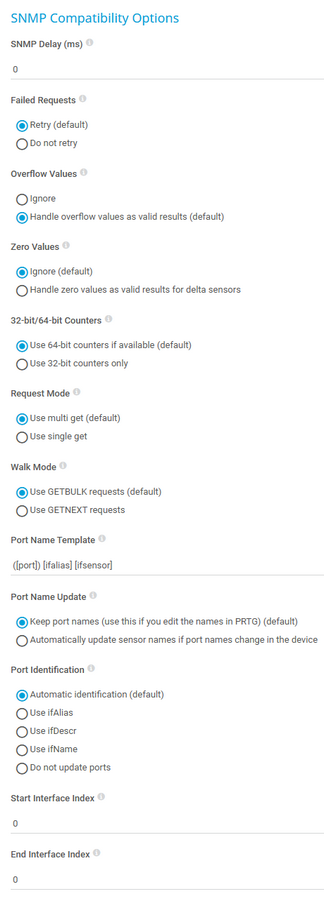
If you experience problems when you monitor via Simple Network Management Protocol (SNMP) sensors, use the following compatibility options for troubleshooting.
Setting |
Description |
|---|---|
SNMP Delay (ms) |
Enter the time in milliseconds (ms) that PRTG waits between two SNMP requests. You can define a delay between 0 and 100. Enter an integer.
|
Failed Requests |
Select if an SNMP sensor tries again after a request fails:
|
Overflow Values |
Select how PRTG handles overflow values. Some devices do not correctly handle internal buffer overflows. This can cause false peaks. PRTG can handle overflow values in two ways:
|
Zero Values |
Select how PRTG handles zero values. Some devices send incorrect zero values. This can cause false peaks. PRTG can handle zero values in two ways:
|
32-bit/64-bit Counters |
Select the type of traffic counters that PRTG searches for on a device:
|
Request Mode |
Select the request method that PRTG uses for SNMP sensors:
|
Walk Mode |
Select the kind of SNMP walk that PRTG uses for SNMP sensors:
|
Port Name Template |
Select how PRTG displays the name of SNMP sensors. Enter a template that uses several variables. When you add new sensors, PRTG scans the interface for available counters at certain OIDs. At each OID, several fields with interface descriptions are usually available. They are different for every device and OID. PRTG uses the information in these fields to name the sensors. If a field is empty or if it is not available, PRTG adds an empty string to the name. By default, the port name template is ([port]) [ifalias] [ifsensor], which creates a name like (001) Ethernet1 Traffic. You can use and combine any field names that are available at an OID of your device, for example:
|
Port Name Update |
Select how PRTG reacts if you change the names of ports in your physical device (for example, a switch or router):
|
Port Identification |
Select the field that PRTG uses for SNMP interface identification:
|
Start Interface Index |
Enter the index at which PRTG starts to query the interface range during sensor creation. Enter 0 for the automatic mode.
|
End Interface Index |
Enter the index at which PRTG stops querying the interface range during sensor creation. Enter 0 for the automatic mode.
|
The settings you define in this section apply to the following sensors:
The proxy settings determine how a sensor connects to a URL. You can enter data for an HTTP proxy server that sensors use when they connect via HTTP or HTTPS.
This setting only applies to sensors and how they monitor. For more information on how to change the proxy settings for the PRTG core server, see section Core & Probes.
The SSL Certificate sensor and the SSL Security Check sensor do not support HTTP proxies but you can configure connections via SOCKS proxies in the sensors' settings:
Setting |
Description |
|---|---|
IP Address/DNS Name |
Enter the IP address or Domain Name System (DNS) name of the proxy server. If you leave this field empty, sensors do not use a proxy.
|
Port |
Enter the port number of the proxy. The default port is 8080. Enter an integer. |
User Name |
If the proxy requires authentication, enter the user name for the proxy login. Enter a string or leave the field empty.
|
Password |
If the proxy requires authentication, enter the password for the proxy login. Enter a string or leave the field empty.
|
Setting |
Description |
|---|---|
Scanning Interval |
Select a scanning interval from the dropdown list that determines the amount of time that the sensor waits between two scans:
|
If a Sensor Scan Fails |
Select the number of scanning intervals that the sensor has time to reach and to check a device again if a sensor scan fails. Depending on the option that you select, the sensor can try to reach and to check a device again several times before the sensor shows the Down status. This can avoid false alarms if the target device only has temporary issues. For previous scanning intervals with failed requests, the sensor shows the Warning status. The following options are available:
|
Schedules, Dependencies, and Maintenance Window
Setting |
Description |
|---|---|
Schedule |
Select a schedule from the list. You can use schedules to monitor during a certain time span (days or hours) every week:
|
Maintenance Window |
Select if you want to set up a one-time maintenance window:
|
Maintenance Begins |
This setting is only visible if you select Set up a one-time maintenance window above. Use the date time picker to enter the start date and time of the one-time maintenance window. |
Maintenance Ends |
This setting is only visible if you select Set up a one-time maintenance window above. Use the date time picker to enter the end date and time of the one-time maintenance window. |
Setting |
Description |
|---|---|
User Group Access |
Select the user groups that have access to the object. You see a table with user groups and group access rights. The table contains all user groups in your setup. For each user group, you can choose from the following group access rights:
To automatically set all child objects to inherit this object's access rights, select the Revert access rights of child objects to "inherited" option.
|
Setting |
Description |
|---|---|
Channel Unit Types |
For each type of channel, select the unit in which PRTG displays the data. If you define this setting on probe, group, or device level, you can inherit these settings to all sensors underneath. You can set units for the following channel types (if available):
|
Setting |
Description |
|---|---|
Unusual Detection |
Select if you want to use the unusual detection for sensors:
|
Similar Sensors Detection |
Select if you want to activate the similar sensors analysis:
|
System Information |
Select if you want to retrieve and show system information for your devices:
|
Save your settings. If you change tabs or use the main menu without saving, all changes to the settings are lost.
KNOWLEDGE BASE
What security features does PRTG include?
How do I set permissions for the Amazon Web Services (AWS) API key to use certain sensors in PRTG?
What is the Overflow Values setting in the SNMP Compatibility Options?
How can I change the defaults for names automatically generated for new SNMP sensors?
Automatically update port name and number for SNMP Traffic sensors when the device changes them