PRTG Manual: Introduction: Monitoring with PRTG
This section shows you how to prepare your IT infrastructure so that you can monitor it with PRTG.
In this section:
- What PRTG Does
- How to Monitor with PRTG
- What PRTG Monitors
- How to Prepare Monitoring
- Which Hardware Do I Want to Monitor
To immediately start monitoring with PRTG, go to section Quick Start Guide.
PRTG is a unified monitoring tool that can monitor almost any object that has an IP address. It consists of the PRTG core server and one or more probes:
- The PRTG core server is responsible for configuration, data management, PRTG web server, and more.
- Probes collect data and monitor processes on devices via sensors.
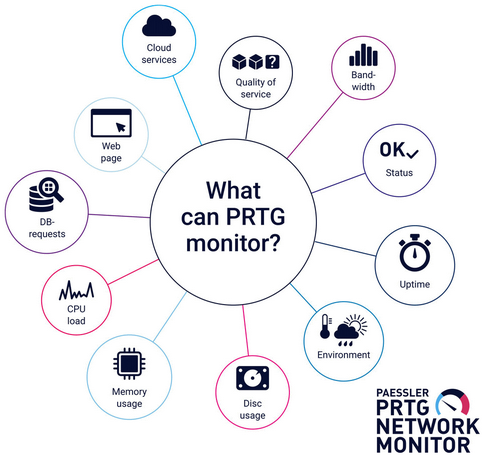
Sensors are the building blocks of PRTG. A sensor can tell you about one or more aspects of a device:
- Uptime
- Load
- Interface throughput
- Bandwidth usage
- Loading times
- Speed
- Hardware status
- Temperature
- Quality
- Resource consumption
- User counts
- Record counts
- Log events
- Database requests
PRTG obtains monitoring data from target devices in the following ways:
- Polls or queries sensor data: PRTG actively gathers data from a device in regular intervals. This includes, for example, device status, resource usage, and performance metrics. Most sensors use this method. PRTG can also consume and collect sensor data based on interfaces with, for example, HTTP or HTTPS requests, port checks, email checks, File Transfer Protocol (FTP) downloads, and database requests.
- Listens for or receives sensor data: PRTG passively receives data from a device or application. This includes, for example, unexpected events, Syslogs and Simple Network Management Protocol (SNMP) traps, detailed data flow, and event log messages.
Most of the monitoring data that PRTG collects is actively queried. It is the basis for statistical sampling to see how a device or application performs over time.
For more information, see section Sensor Technologies.
PRTG comes with hundreds of sensors.They range from platform-specific sensors to generic hardware and bandwidth sensors. Some of them are preconfigured to immediately gather monitoring data from their target devices. You can also create custom sensors or write custom scripts that return data from applications. Visit the PRTG Sensor Hub to learn more about ready-to-use custom sensors.
For more information, see section Available Sensor Types.
The first step in comprehensive monitoring is to make a plan. Think about the following questions:
- What do I need to monitor in my IT infrastructure?
- How can I retrieve the needed information? Which technologies and credentials are required?
- Which notification methods do I want to use to receive alerts if something is wrong?
Which Hardware Do I Want to Monitor?
We recommend that you start with your Business Critical Tier-1. This usually includes the core network and other infrastructure that all network devices depend upon:
- Key infrastructure, such as core routers, switches, VPN and firewalls
- Basic network services, such as Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS)
- Authentication, like Lightweight Directory Access Protocol (LDAP)
Use the following list to help you plan the monitoring of your IT infrastructure with PRTG:
- Core infrastructure
- Routers, switches, firewalls
- Core network services: DNS, Active Directory (AD), LDAP servers
- For your hardware devices, you need statistics on availability, usage, and performance.
- PRTG retrieves data via standard protocols:
- Ping, SNMP; web queries via HTTP and HTTPS; email via Post Office Protocol version 3 (POP3), Internet Message Access Protocol (IMAP), Simple Mail Transfer Protocol (SMTP)
- Hardware parameters via SNMP, Secure Shell (SSH), Simple Object Access Protocol (SOAP)
- Bandwidth usage via Flow (NetFlow, jFlow, sFlow, IPFIX), packet sniffing, SNMP
- Windows systems via Windows Management Instrumentation (WMI)
- Other interfaces via SSH and scripts (for example, PowerShell and Python)
KNOWLEDGE BASE
My SNMP sensors don’t work. What can I do?
My WMI sensors don't work. What can I do?
My HTTP sensors don't work. What can I do?
How can I send SMS text message notifications via a modem or a mobile phone with PRTG?
How can I use push notifications with PRTG?
VIDEO TUTORIAL
SNMP Trap receiver and syslog receiver sensors
Notifications