Custom alerts and data visualization let you quickly identify and prevent infrastructure issues.
Network infrastructure monitoring is a vital part of a smooth-running business. You can only guarantee performance if all servers are up and running, switches and routers are functioning properly, and virtual machines are error-free. Monitor every connected device on your network with Paessler’s PRTG monitoring software – a single solution to keep you sane and your entire IT environment safe and reliable.
When software bugs or hardware fails, you have to move quickly. PRTG is a never-resting observer – its only job is to catch issues and alert you before they become business-critical.
PRTG quickly detects network activity that might point to a security threat or potential system failure. With detailed information on your network traffic, bandwidth usage, and device performance, it’s easy to isolate problems and target your response for faster resolution.
Get the alerts that fit your infrastructure. With PRTG’s more than 250 built-in sensors and powerful API, you can easily customize your monitoring setup to suit your organization’s unique needs.
PRTG lets you modify individual sensors and alerts with just a few clicks. You can integrate with other systems, configure task automations, and get real-time insights that let you pounce on potential issues before they escalate.
Say goodbye to the jumble of mismatched monitoring tools and hello to our all-in-one network monitoring software. PRTG helps seal weak spots and makes things less complicated by replacing your various tools and bringing your monitoring data together into a single dashboard.
The result? A network that's easier to manage and tougher to crack.
Diagnose network issues by continuously tracking your IT infrastructure – no matter if it’s on-premises or if you have a cloud infrastructure. Show response time, bandwidth, CPU usage, and other infrastructure performance metrics in real time. Visualize monitoring data in clear graphs and dashboards to identify problems more easily. Gain the overview you need to troubleshoot all kinds of network infrastructure issues.
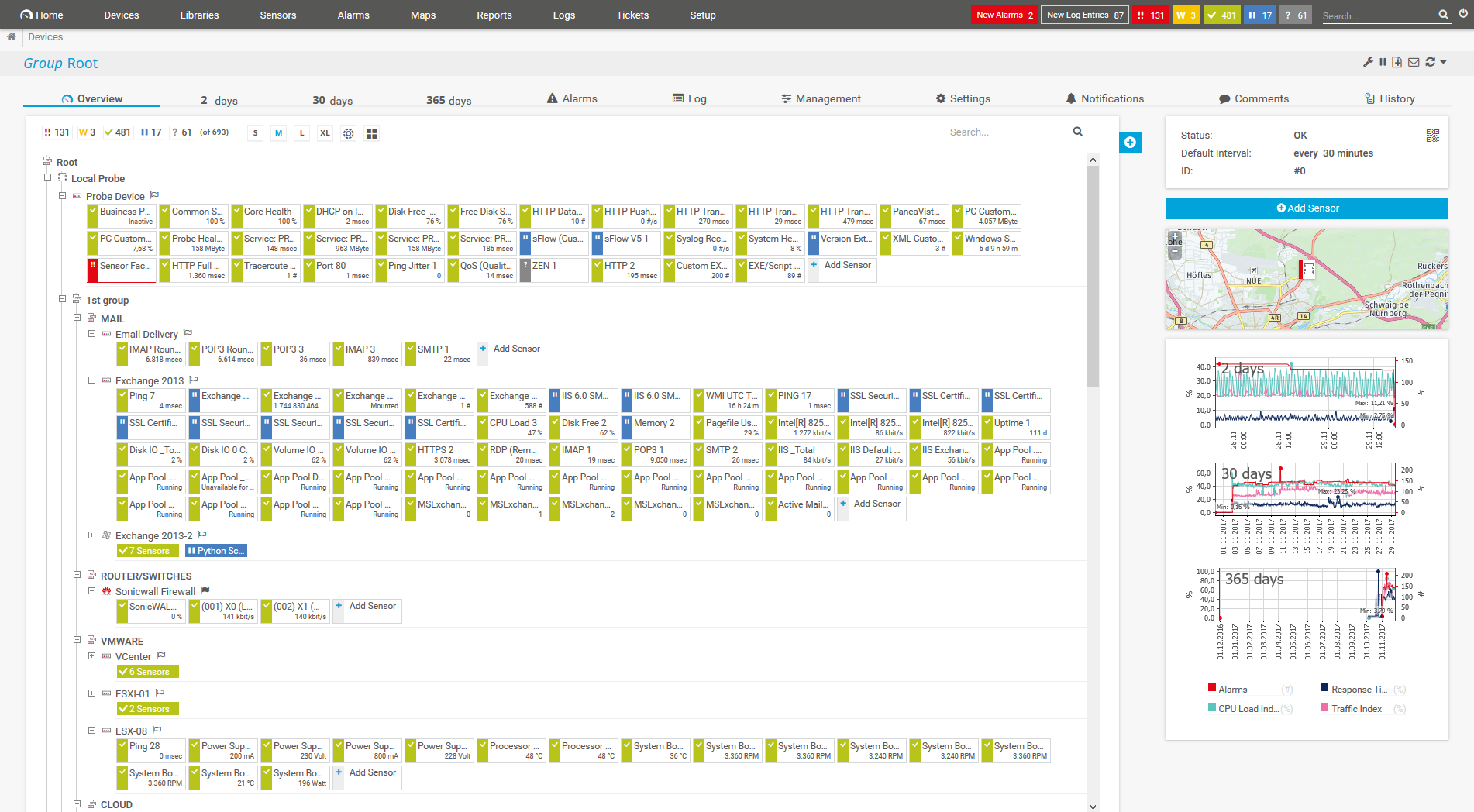
Device tree view of the complete monitoring setup

Custom PRTG dashboard for keeping an eye on the entire IT infrastructure

Sunburst view of a device tree
PRTG provides comprehensive monitoring for your entire IT infrastructure, including servers, virtual environments, cloud services, and all kinds of network devices like servers, routers, switches, or firewalls.
This big-picture approach helps you catch any weak links and immediately spot potential bottlenecks.
PRTG keeps tabs on all the VIPs in your network – uptimes, downtimes, system health, bandwidth usage, virtual servers, applications, and more.
It even sorts out network traffic, checks on service quality, and spots any odd behavior across devices and users.
With PRTG's real-time infrastructure monitoring, you're always up to speed on your network's mood – whether you're at your desk or on the beach.
Graphs and dashboards show server status, while the mobile app and automatic alerts keep you ready to tackle issues anytime, anywhere.
Installing PRTG is a breeze. As an agentless solution, it saves you time and hassle, allowing your IT team to focus on more critical tasks.
PRTG’s built-in alarm system sends instant notifications via email, SMS, or push notification at the first sign of trouble, helping to prevent or minimize system failures.
PRTG comes with more than 250 native sensor types for monitoring your entire on-premises, cloud, and hybrid cloud environment out of the box. Check out some examples below!
See the PRTG Manual for a list of all available sensor types.
Custom alerts and data visualization let you quickly identify and prevent infrastructure issues.
PRTG is set up in a matter of minutes and can be used on a wide variety of mobile devices.

“Excellent tool for detailed monitoring. Alarms and notifications work greatly. Equipment addition is straight forward and server initial setup is very easy. ...feel safe to purchase it if you intend to monitor a large networking landscape.”
Partnering with innovative IT vendors, Paessler unleashes synergies to create
new and additional benefits for joined customers.
With ScriptRunner Paessler integrates a powerful event automation platform into PRTG Network Monitor.
By integrating PRTG with Martello iQ, you can add a fast analytics layer to improve uptime, visualize your IT environment, and integrate all of your IT systems into a single pane of glass.
Siemon and Paessler bring together intelligent building technology and advanced monitoring and make your vision of intelligent buildings and data centers become reality.
Real-time notifications mean faster troubleshooting so that you can act before more serious issues occur.
Network Monitoring Software – Version 26.1.116.1532 (February 9th, 2026)
Download for Windows and cloud-based version PRTG Hosted Monitor available
English, German, Spanish, French, Portuguese, Dutch, Russian, Japanese, and Simplified Chinese
Network devices, bandwidth, servers, applications, virtual environments, remote systems, IoT, and more
Choose the PRTG Network Monitor subscription that's best for you

Network infrastructure monitoring is the process of overseeing and managing the hardware and software components of a network to ensure their optimal performance, availability, and security. This involves continuously tracking various elements of the network infrastructure, including servers, routers, switches, firewalls, and other network devices, as well as the applications and services running on them.
Key aspects of network infrastructure monitoring include:
Monitoring your network infrastructure is crucial to ensure its optimal performance, security, and reliability. Here are some reasons why you should monitor your network infrastructure:
PRTG covers physical, virtual, and cloud environments, ensuring comprehensive monitoring of your entire infrastructure. It seamlessly integrates with various environments, providing a unified view of your network’s health.
Absolutely! PRTG is adaptable to any infrastructure size, from a few devices to a large-scale environment. Flexible licensing and pricing ensure scalability. Whether your network is growing or you need to scale down, PRTG adjusts to fit your needs.
While PRTG is no dedicated network security software, it complements your existing security measures. Ensure, for example, that antivirus software is installed on your network to protect against malware and viruses. PRTG focuses on monitoring and detecting anomalies that could indicate a security threat, providing an additional layer of defense.
In PRTG, “sensors” are the basic monitoring elements. One sensor usually monitors one measured value in your network, for example the traffic of a switch port, the CPU load of a server, or the free space on a disk drive. On average, you need about 5-10 sensors per device or one sensor per switch port.
Paessler conducted trials in over 600 IT departments worldwide to tune its network monitoring software closer to the needs of sysadmins. The result of the survey: over 95% of the participants would recommend PRTG – or already have.
Paessler PRTG is used by companies of all sizes. Sysadmins love PRTG because it makes their job a whole lot easier.
Bandwidth, servers, virtual environments, websites, VoIP services – PRTG keeps an eye on your entire network.
Everyone has different monitoring needs. That’s why we let you try PRTG for free.