By default, PRTG uses its own internal user account database to authenticate users. For many PRTG customers, particularly those with smaller networks, this local authentication meets all their needs.
But for PRTG customers who have more complex environments and infrastructures or who want to reduce the number of authentication mechanisms in their networks, PRTG offers Active Directory (AD) integration as well.
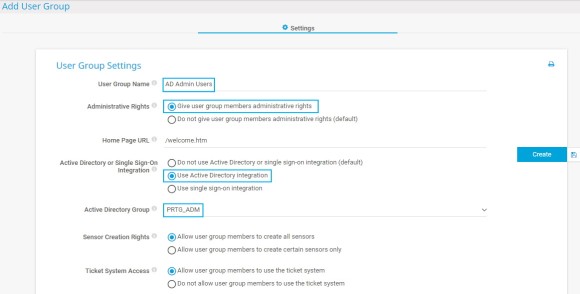
This way, all members of the AD user groups that are mapped to user groups in PRTG during the integration can log in to PRTG with their AD domain credentials afterward.
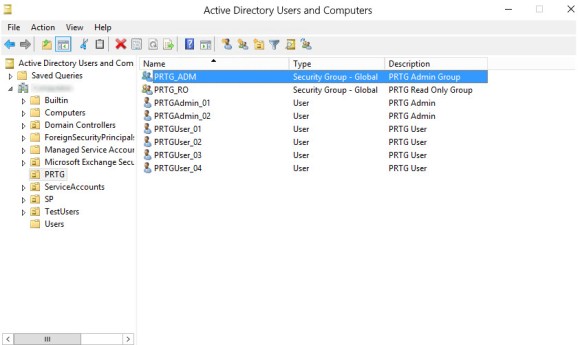
In the AD, make sure that users who require the same access rights for PRTG are in the same AD user group.
In our example, the AD user group PRTG_ADM contains the two administrator user accounts that later have administrative rights in PRTG and that can also manage access rights and cluster setups and change the monitoring configuration of PRTG. The AD user group PRTG_RO contains the four user accounts that later have only read access rights in PRTG.
Get full visibility with real-time dashboards, alerts, and customizable sensors
Make sure that the PRTG core server system is a member of the AD domain with which you want to integrate it. You can check and, if necessary, change this setting via the Windows Control Panel:
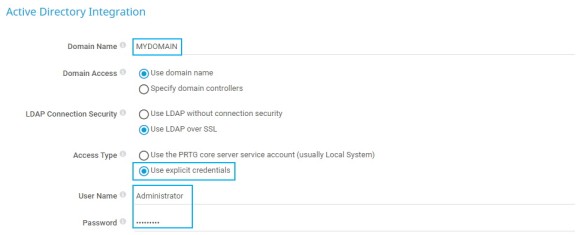
In the next step, you need to provide your local AD domain details in PRTG:
Custom alerts and data visualization let you quickly identify and prevent all kinds of issues
Repeat these steps for the PRTG_RO user group to create a second group of users that have only read access rights for PRTG. In this case, leave the default setting under Administrative Rights.
Now, members of the defined AD groups can log in to PRTG with the respective access rights.
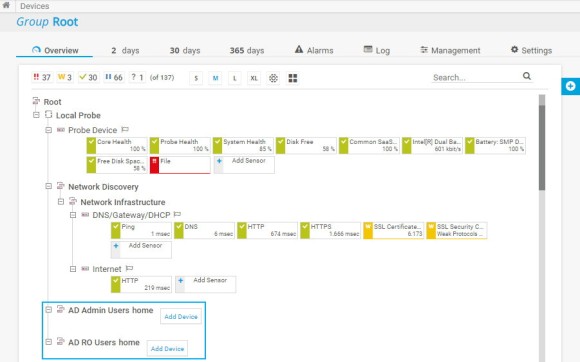
In the device tree, PRTG automatically creates new groups with the name [group_name] home for each of the integrated AD user groups.
Do not forget to set group access rights that apply to device tree objects as well as to libraries, maps, and reports. You can do so in an object’s settings in section Access Rights.
The easiest way is to set group access rights in the settings of the root group.